SAML Concepts: Difference between revisions
| Line 30: | Line 30: | ||
There is a ''trust relationship'' between the Identity Provider and and the Service Provider. | There is a ''trust relationship'' between the Identity Provider and and the Service Provider. | ||
=Token= | =Token= | ||
Revision as of 05:43, 21 February 2017
Internal
Subject
Subjects are entities that have identity related information specific to a security domain.
Principal
Pseudonyms
SAML uses pseudonyms to provide a privacy-enabling "alias" for global identifiers, to avoid collisions between service providers. The pseudonyms are opaque pseudo-random identifiers, with no discernible correspondence with meaning identifiers such as e-mail addresses, between service providers to represent principals.
Security Domain
Identity Provider
The Identity Provider (IdP) is.
The Identity Provider is also known as a security provider or the asserting party.
Service Provider
The Service Provider (SP) is ....
The Service Provider is also known as the relying party.
Trust Relationship
There is a trust relationship between the Identity Provider and and the Service Provider.
Token
A SAML token is a type of token issued by a STS/IdP that can be used to enable SSO. A relying resource secured by SAML will redirect users to SAML identity provider to obtain a valid SAML token before authenticating and authorizing the user.
Single Sign-On (SSO)
Single sign-on (SSO) is not strictly a SAML concept. However, because SAML provides a trusted way to share security information, applications using SAML can participate in single sign-on scenario where the identity of a subject is verified by a party and other party uses it because it trusts the first party and the communication mechanisms between them. SAML requires the user to enroll with at least one SAML-enabled security provider. The identity of the user will be verified (authenticated) by that security provider. Web browser single sign-on is a SAML profile.
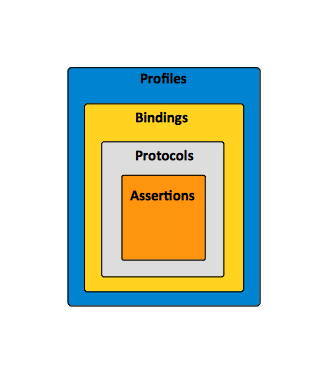
SAML Profile
A profile is essentially a use case for SAML. A profile combines assertions, protocols and bindings to support specific use cases. For example, the Web Browser SSO Profile specifies how SAML authentication assertions are communicated between an Identity Provider and Service Provider to enable single sign-on for a browser user. From a high level perspective, several notable SAML use cases are Web Browser Single Sign-On, Attribute-based Authorization, Identity Federation and WS-Security.
For more details on SAML profiles, see:
SAML Binding
SAML protocol bindings are the mappings from SAML request/response message exchanges into standard messaging or communication protocols. For more details see:
SAML Protocol
A SAML protocol is represented by the sequence of requests and responses for obtaining assertions and performing identity management.
SAML Assertion
The SAML assertion is an XML fragment transferred between the security providers and the service providers containing statements that applications and service providers use to make authentication and authorization decisions. Assertions include:
- Authentication statements
- Attribute statements
- Authorization decision statements
Authentication Context
Detailed data on types and strengths of Authentication.
Metadata
Metadata is an XML document that specifies configuration for IdPs and SPs. Configuration elements:
- endpoint of the single sign on
- expect request/response with signature
- support bindings of request/response (GET/POST)
- X.509 Certificate used for signature and verification
SAML metadata specify how configuration and trust-related data can be more easily deployed in SAML systems. Identity providers and service providers often need to agree on data such as roles, identifiers, and supported profiles. SAML metadata provides a structure for identifying the actors involved in the various profiles, such as single sign-on identity provider, attribute authority, and requester.
Standards SAML 2.0 Relies On
- XML Schema
- XML Signature
- XML Encryption
- HTTP
- SOAP
SAML Architecture
To Deplete
- https://home.feodorov.com:9443/wiki/Wiki.jsp?page=SingleSignOn
- https://home.feodorov.com:9443/wiki/Wiki.jsp?page=PicketLinkSAMLSSO#section-PicketLinkSAMLSSO-Concepts