Iptables Concepts
Internal
Overview
iptables is capable of tracking a connection's state. For more details see How State Machine Connection Tracking Works.
iptables is specifically built to work on the headers of the Internet and the Transport layers. It is possible to do some very basic filtering Application and Network access layers as well, but iptables was not designed for this, nor is it very suitable for those purposes. iptables does not do string matching, because a specific string can be spread across several packets, and assembling data from different packets is too processor and memory intensive.
It's always a good idea to have an iptables configuration in place on a given machine, regardless of outside firewalls you may have. Each individual machine, depending on its uses, might have different packet filtering needs. As a result of this, the external firewall device should have a configuration that permits everything the most permissive of your local systems is going to need to do: each individual machine, then, can deny as much of that as it can get away with, without sacrificing its critical functionality.
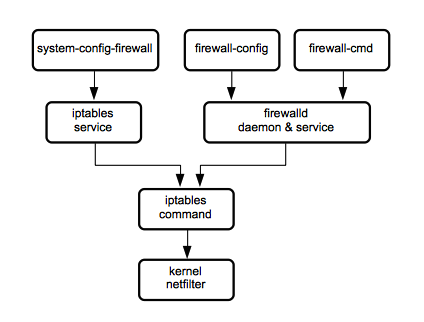
netfilter, iptables tool, iptables service and firewalld
netfilter
netfilter is a set of hooks inside the Linux kernel that allows kernel modules to register callback functions with the network stack. A registered callback function is then called for every packet that traverses the respective hook.
iptables
iptables is a Linux userspace command line tool that manipulates the IPv4 network packet filtering tables and rules. Packet filtering is most commonly used to implement firewalling functionality. It is also used to implement Network Address Translation (NAT). The iptables command is known to yum as "iptables". For more usage details see iptables Command Line Tool.
ip6tables
ip6tables is the equivalent command line tool that manipulates the IPv6 network packet filtering rules. For more usage details, see iptables Command Line Tool.
iptables and ip6tables Services
iptables and ip6tables services are systemd services that use the iptables tool to interact with the kernel netfilter framework. The iptables services are known to yum as "iptables-services". There are two parallel configurations for iptables and ip6tables services.
firewalld
firewalld is a firewall service daemon with D-BUS interface. More details about firewalld available here:
iptables service and firewalld
The iptables service and firewalld are incompatible, you must use one or another.
This is how fiewalld is prevented to start at boot.
Older Firewall Implementations
ipchains
ipfwadm
Network Packet Filtering
Every network packet arriving from the network interfaces and every packet originating from applications are passed to iptables, which decides what to do with each one of them. iptables uses the concept of IP addresses, protocols and ports. For a particular packet, only one of the INPUT, OUTPUT or FORWARD chains are used.
Packet Handing Details
iptables State Machine
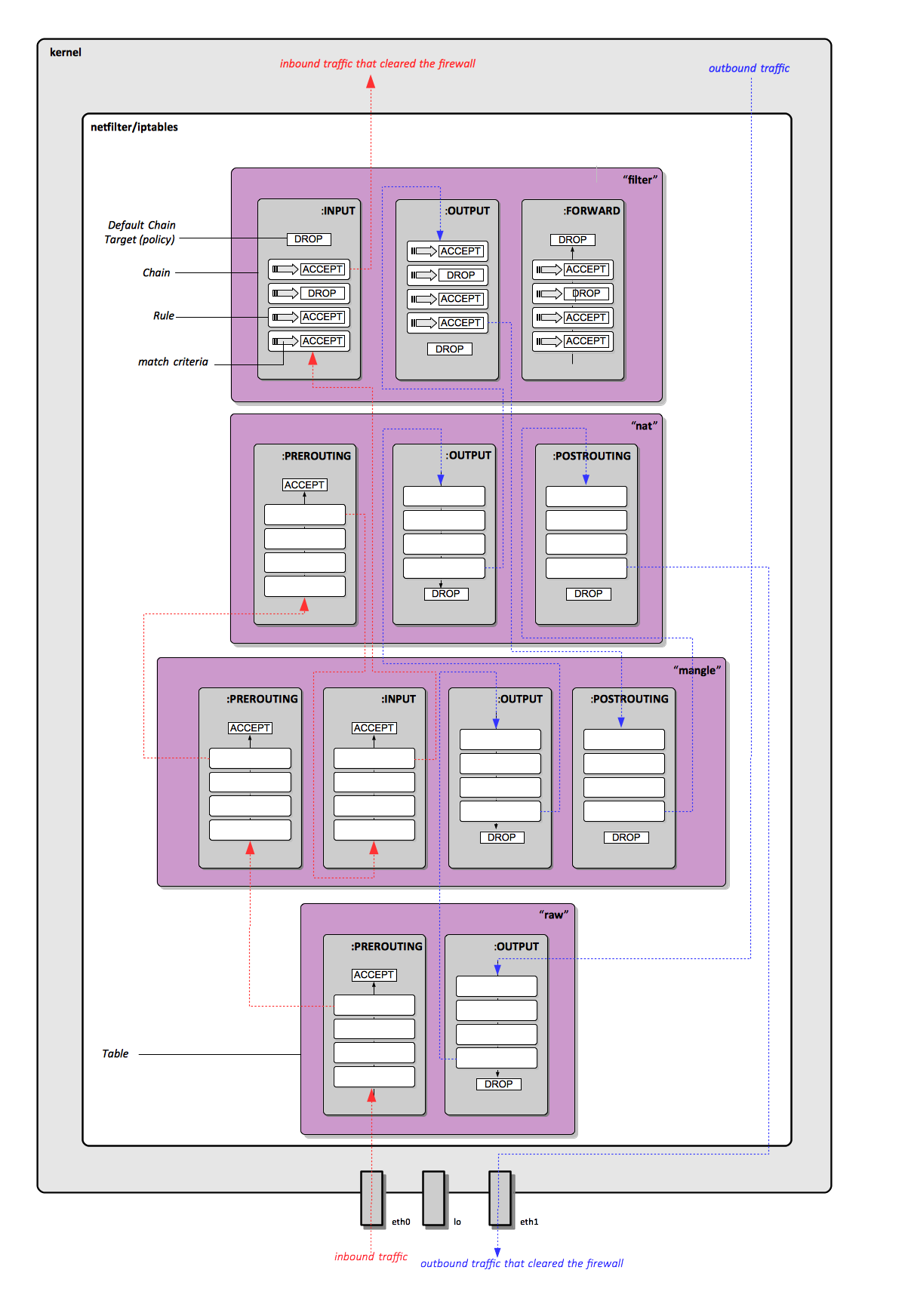
Table
An iptables table is a data structure that contains a number of built-in chains and may also contain user-defined chains. Several different tables may be defined. Once it is decided a packet is matched against a certain table, the packet is matched against rules contained by that tables' chains. The chains are picked depending on where the packets comes from and the chain semantics. For more details see iptables Packet Handling Details.
The default table acted upon by the iptables command is "filter". The target table can be changed with -t.
Active tables at a certain moment:
cat /proc/net/ip_tables_names
Default tables:
filter
This is the default table iptables interacts with. To change that use the '-t' option. The "filter" tables contains the built-in chains INPUT, FORWARD and OUTPUT. For more details on how packets interact with tables see :iptables Packet Handling Details.
nat
This table is consulted when a packet that creates a new connection is encountered. It contains the built-in chains PREROUTING, OUTPUT and POSTROUTING. For more details on how packets interact with tables see iptables Packet Handling Details.
mangle
This table is used for specialized packet alteration. It contains PREROUTING, OUTPUT, INPUT, FORWARD, POSTROUTING.For more details on how packets interact with tables see :iptables Packet Handling Details.
raw
This table is used mainly for configuring exemptions from connection tracking in combination with the NOTRACK target. It registers at the netfilter hooks with higher priority and is thus called before ip_conntrack, or any other IP tables. It provides the following built-in chains PREROUTING and OUTPUT. For more details on how packets interact with tables see :iptables Packet Handling Details.
Chain
Each chain is a list of firewall rules that can match packets. The first rule added with -A (or the rule inserted with -I 1) is the first rule in the chain, the rule packets are matched against first. Once a packet is sent to a specific chain, it is matched in order against the rule criteria. If a packet does not match a rule's criteria, it is sent to the next rule in the chain, and so on until the default target of the chain is applied to the packet (the chain's default policy).
The INPUT chain should usually be configured with a DROP default policy (anything that is not explicitly permitted is dropped).
The OUTPUT chain should usually be configured with an ALLOW default policy (anything that is not explicitly denied is allowed)
Chains:
INPUT
The chain handling packets arriving from the network interfaces.
OUTPUT
Chain handling packets generated locally; handling takes place before routing
FORWARD
Chain for packets neither destined for, nor originating from this host, but routed through it. Handles packets coming from one NIC and going to other NIC. This chain is used if you use your computer as a router.
PREROUTING
Chain for for altering packets as soon as they come in, before routing.
POSTROUTING
For altering packets as they are about to go out - after routing. Packet translation happens when the packets are leaving the system.
Rule
A firewall rule specifies criteria for a packet and a target for the packets that match the criteria. If a packet matches the criteria, the corresponding target is applied, and it is not processed by further rules in the chain. If the criteria is not matched, the packet is matched against the next rule.
Target
A target defines what iptables does with packet that matched a rule's criteria. A target may be a jump to a user-defined chain in the same table or one of the special values ACCEPT, DROP, QUEUE or RETURN. More about targets: http://www.frozentux.net/iptables-tutorial/iptables-tutorial.html#TARGETS.
ACCEPT
ACCEPT means to let the packet through (in to the kernel or out to the network interface).
DROP
DROP means to discard the packet. Dropping/denying usually mean simply deleting the packet, with no further actions being taken. There is no reply to tell the originating host what happened.
QUEUE
QUEUE means to pass the packet to userspace, via the queue handler.
RETURN
RETURN means stop traversing this chain and resume at the next rule in the previous (calling) chain.
LOG
REJECT
Rejecting is similar to denying, with the exception that a notification is sent to the originating host.
... REJECT --reject-with icmp-host-prohibited ...
REDIRECT
The REDIRECT target is used to redirect packets and streams to the machine itself. This means that we could REDIRECT all packets destined for the HTTP ports to an HTTP proxy like squid, on our own host. Locally generated packets are mapped to the 127.0.0.1 address. In other words, this rewrites the destination address to our own host for packets that are forwarded, or something alike. The REDIRECT target is extremely good to use when we want, for example, transparent proxying, where the LAN hosts do not know about the proxy at all.
Note that the REDIRECT target is only valid within the PREROUTING and OUTPUT chains of the nat table. It is also valid within user-defined chains that are only called from those chains, and nowhere else. The REDIRECT target takes only one option, as described below.
--to-ports
Example:
iptables -t nat -A PREROUTING -p tcp --dport 80 -j REDIRECT --to-ports 8080
The --to-ports option specifies the destination port, or port range, to use. Without the --to-ports option, the destination port is never altered. This is specified, as above, --to-ports 8080 in case we only want to specify one port. If we would want to specify a port range, we would do it like --to-ports 8080-8090, which tells the REDIRECT target to redirect the packets to the ports 8080 through 8090. Note that this option is only available in rules specifying the TCP or UDP protocol with the --protocol matcher, since it wouldn't make any sense anywhere else.