AWS Elastic Load Balancing Concepts
External
- https://docs.aws.amazon.com/elasticloadbalancing/index.html#lang/en_us
- Using static IP addresses for Application Load Balancers
Internal
Overview
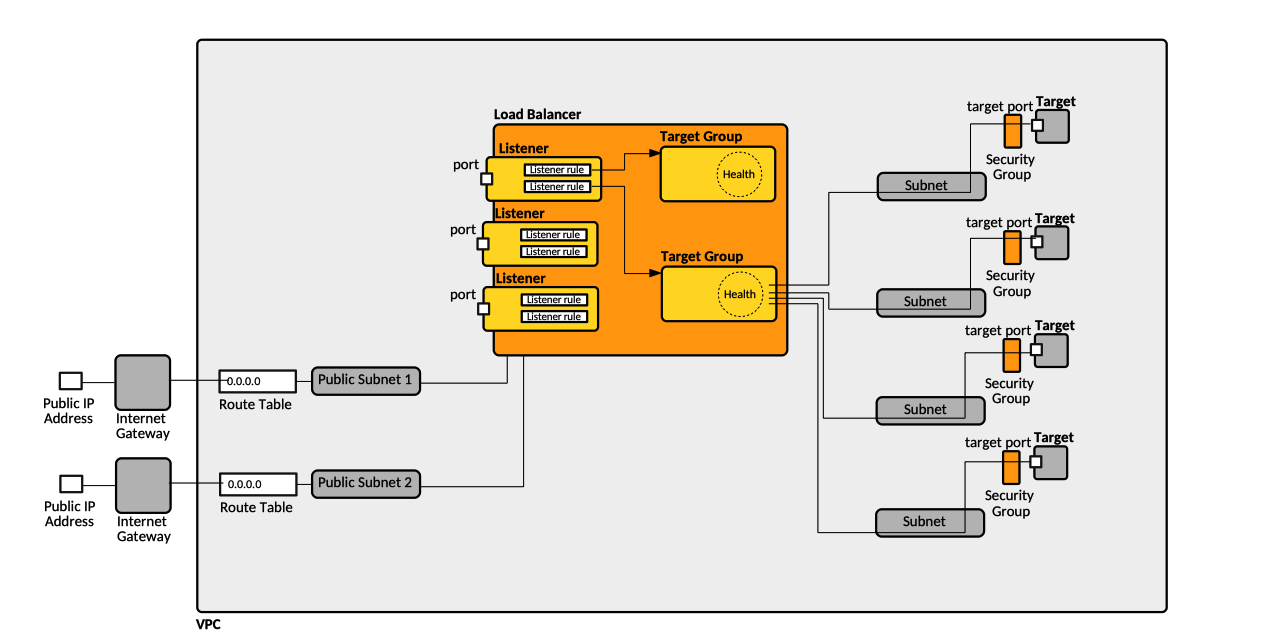
Load Balancer, Listener and Target Group Relationship
Load Balancer
A load balancer serves as the single point of contact for clients, and distributes incoming requests arriving from clients to multiple targets, which actually know how to handle requests and provide responses - the load balancer doesn't, it only knows how to forward requests. This arrangement increases the availability of the application. There are several types of load balancers: application load balancer, network load balancer and classic load balancer. The incoming traffic arrives into the load balancer though one or more listeners, which forward traffic to targets associated with target groups.
Load Balancer Name
The name of a load balancer must be unique within the set of Application Load Balancers and Network Load Balancers for the region. Other documentation section says it must be unique within the AWS account. I can have a maximum of 32 alphanumeric characters and hyphens. A name can't begin with a hyphen. It should not start with "internal-". When creating the load balancer, the name is not required, if missing it will be generated.
Load Balancer Node
A load balancer may have one or more nodes, each node being associated with an availability zone. By default, the node distributes traffic to targets across registered targets in its availability zone only. If cross-zone load balancing is enabled, each load balancer n ode distributes traffic across registered targets in all enabled availability zones.
Load Balancer Scheme
Internet-Facing
An Internet-facing load balancer routes requests from clients running on the public Internet, to targets, which may or may be not public. The nodes of an Internet-facing load balancer have public IP addresses. The DNS name of an Internet-facing load balancer is publicly resolvable to the public IP addresses of the nodes. Therefore, Internet-facing load balancers can route requests from clients over the internet. If the scheme is not specified, "internet-facing" is the default.
Note that simply declaring a load balancer "internet-facing" does not automatically make it publicly accessible. The load balancer must be associated with at least one public subnet - two public subnets, in two different availability zones, in case of application load balancers. See Connecting Internet-Facing Load Balancer to Private IP Address Targets for practical details.
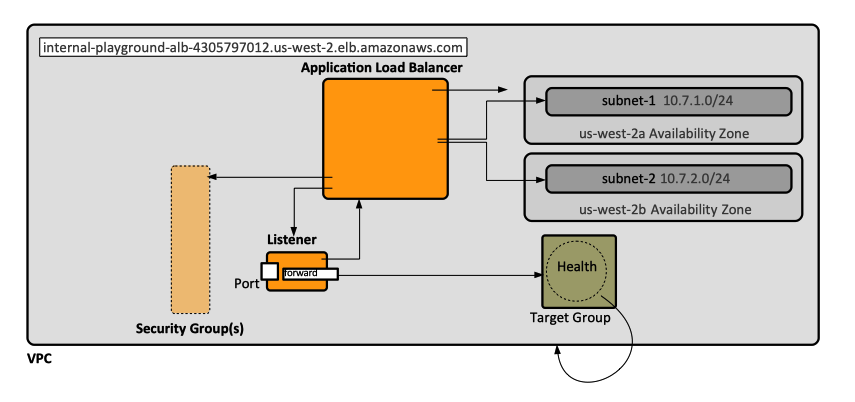
Internal
The nodes of an internal load balancer have only private IP addresses. The DNS name of an internal load balancer is publicly resolvable to the private IP addresses of the nodes. Therefore, internal load balancers can only route requests from clients with access to the VPC for the load balancer.
Load Balancer Types
Used by Amazon ECS.
Application Load Balancer
An Application Load Balancer offers Layer 7 features for the HTTP and HTTPS traffic, like HTTPS offloading. ALBs scale automatically to adapt to changes in traffic. However, they do so with the side effect of changing the IP addresses they bind to. This normally shouldn't be a problem if the ALB is referred to by its DNS name. Application Load Balancers allow containers to use dynamic host port mapping (multiple tasks allowed per container instance). Multiple services can use the same listener port on a single load balancer with rule-based routing and paths.
When an application load balancer uses more than one subnet, each subnet must be deployed in a different availability zone.
Application Load Balancer Configuration
The following configuration parameters are specific to application load balancers:
- idle_timeout.timeout_seconds: the idle timeout value, in seconds. The valid range is 1-4000 seconds. The default is 60 seconds.
- routing.http2.enabled: indicates whether HTTP/2 is enabled. The value is true or false. The default is true.
Application Load Balancer and Security Groups
An application load balancer can be assigned a list of security groups. Why a list? How we select? Care should be taken to make sure the security group allows access to the ports exposed by application load balancer's listeners.
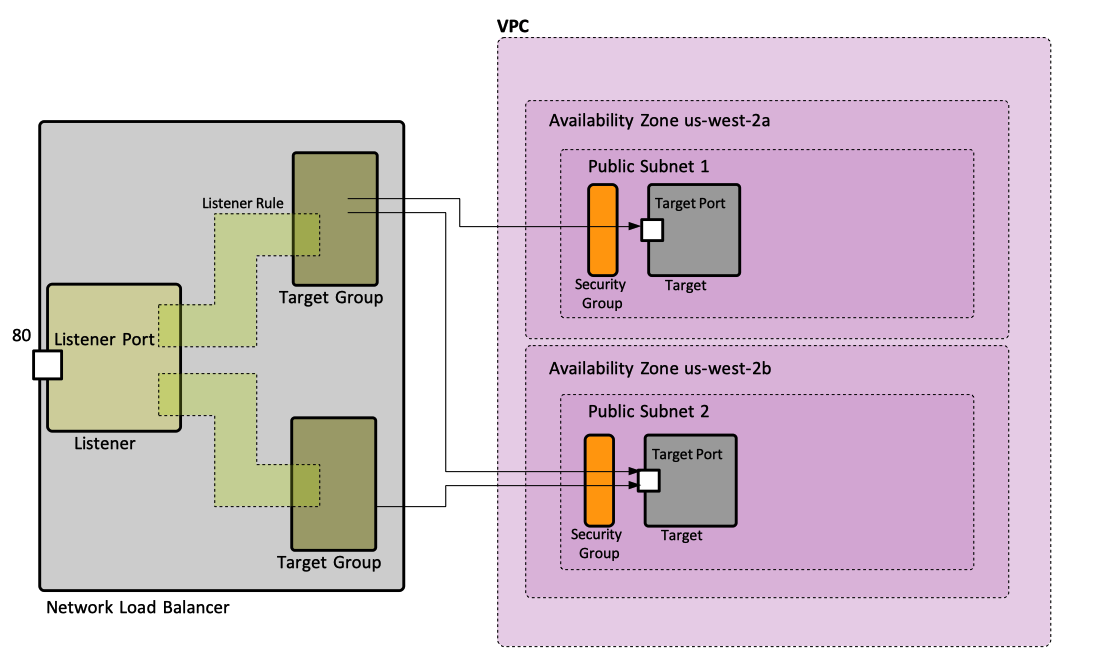
Network Load Balancer
A Network Load Balancer functions at the fourth layer of the Open Systems Interconnection (OSI) model, namely TCP. NLBs offer static IP addresses for each availability zone. After the load balancer receives a request, it selects a target from the target group for the default rule using a flow hash routing algorithm, based on the protocol, source IP address, source port, destination IP address, destination port, and TCP sequence number, and then attempts to open a TCP connection to the selected target. It can handle millions of requests per second.
Elastic Load Balancing creates a network interface for each Availability Zone you enable. Each load balancer node in the Availability Zone uses this network interface to get a static IP address. When you create an Internet-facing load balancer, you can optionally associate one Elastic IP address per subnet. Also see Load Balancers and Availability Zones.
Network Load Balancer Configuration
The following configuration parameters are specific to network load balancers:
- load_balancing.cross_zone.enabled indicates whether cross-zone load balancing is enabled. The value is true or false. The default is false.
Network Load Balancer Operations
Network Load Balancer and EKS
Classic Load Balancer
Common Load Balancer Configuration
access_logs.s3.enabled
access_logs.s3.bucket
access_logs.s3.prefix
deletion_protection.enabled
Application Load Balancer-Specific Configuration
Network Load Balancer-Specific Configuration
IP Address Type
Represents the type of IP addresses that are used by the load balancer's subnets, such as "ipv4" or "dualstack" (for IPv4 and IPv6 addresses). The default value is 'ipv4'. Only for application load balancers?
Subnet Mapping
VPC Association
A load balancer belongs to a VPC and only one. Specifying a subnet implicitly associates the load balancer with the VPC the subnet is part of. If more than one subnet is specified, all subnets must belong to the same VPC, otherwise the load balancer cannot be created.
Load Balancer and Availability Zones
The load balancer routes traffic to the targets from availability zones specified in its configuration. All availability zones belong to one VPC, specified in the configuration. Only one subnet per availability zone can be specified. One Elastic IP per availability zone can also be specified, if a specific addresses is required for the load balancer.
Load Balancer Routing
Configuring a load balancer's routing consists in defining target groups, including the ports and protocols associated with those target groups.
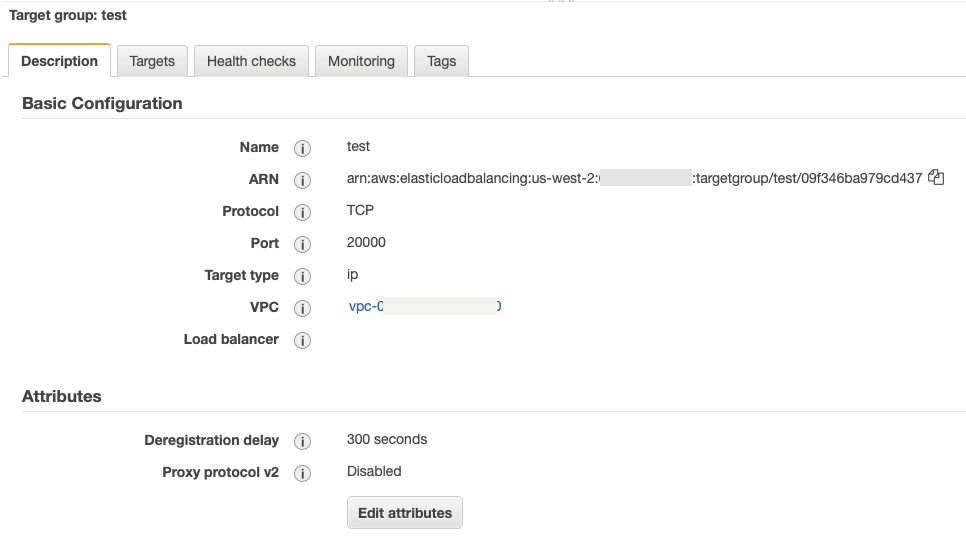
Target Group
A target group is .... The main job of a target group is to be aware of the health of its targets, detect failing targets and remove them from the group.
I don't think this is true:A target group can be associated with at most one listener in a load balancer, hence with at most one load balancer.
A target group may exist in isolation, without being associated with any load balancer. That state is not an invalid state, but it is probably a useless state. The listener/target group association takes the shape of a listener rule: the listener knows about the target group, but the target group does not know about the listener (or load balancer for that matter). The target group only knows about the VPC.
There must be at least one target group per load balancer. If just one target group exists, it is the default target group.
A target group routes requests to one or more registered targets, which can be EC2 instances or other types of request-serving endpoints, using a pre-configured TCP protocol and the port. A target can be registered with multiple target groups. A target group supports health checks: health checks are performed on all target registered to a target group that is specified on a listener rule for the load balancer.
Target groups are relevant for AWS CodeDeploy deployments groups, where they are used to route traffic during a deployment.
Target Group Name
Target Group VPC Association
The target group must be associated with one and only one VPC, by specifying the VPC ID, which is required.
Target Group Protocol
The protocol used when routing traffic to the targets.
Target Group Port
The port on which the targets receive traffic.
Target Group Port vs Target Port
There is actually no target group port, in that the target group does not listen to a port. Target group port actually means "target port".
Target Type
When registering a target with a target group, the target must specify its type, and the group's Target Type establishes accepted types for this group. A group can have only one Target Type. Only target of type "Target Type" can be registered with the group. Valid types: instance, ip and lambda.
Instance
The target is specified by the instance ID. This is the default value.
IP
The target type is specified by an IP address. The IP address can be specified from one of the following CIDR blocks:
- the subnets of the VPC for the target group.
- 10.0.0.0/8 (RFC 1918)
- 100.64.0.0/10 (RFC 6598)
- 172.16.0.0/12 (RFC 1918)
- 192.168.0.0/16 (RFC 1918)
Publicly routable IP addresses can't be specified.
Lambda
The target groups contains a single Lambda function.
Target
A target is usually an Amazon EC2 instance, but it can also be "serverless" containers launched using FARGATE launch types in ECS clusters.
A target can be registered with multiple target groups.
Target Groups and ECS FARGATE Targets
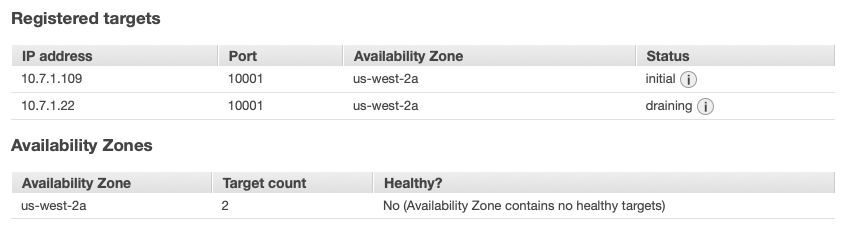
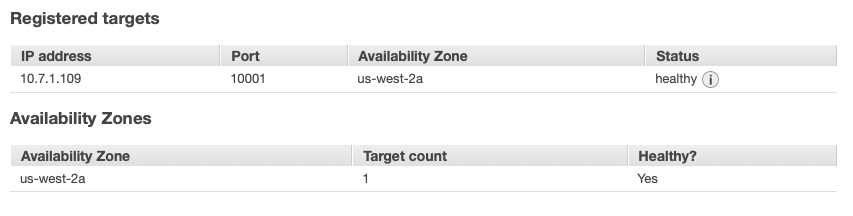
A target group to send traffic into ECS FARGATE targets should be of type "ip". The target group should be available when the ECS service is created, and the targets are correctly registered even if they get dynamic IP addresses. More than that, if the ECS task is stopped, the target group adjusts automatically:
After a while:
Health Checks
Health checks are configured on a per-target group basis. A health check configured on a target group is performed on all targets registered with that target group.
Health Check Protocol
The protocol that the load balancer uses when performing health checks on the targets. Valid values: HTTP, HTTPS, TCP, TLS. For Application Load Balancers, the default is HTTP. For Network Load Balancers, the default is TCP. The TCP protocol is supported for health checks only if the protocol of the target group is TCP or TLS. The TLS protocol is not supported for health checks.
Health Check Interval
The approximate number of seconds between health checks for an individual target. For Application Load Balancers, the range is 5–300 seconds. For Network Load Balancers, the supported values are 10 or 30 seconds. If the target type is instance or ip, the default is 30 seconds. If the target type is lambda, the default is 35 seconds.
Health Check Timeout
The amount of time, in seconds, during which no response from a target means a failed health check. For Application Load Balancers, the range is 2–120 seconds and the default is 5 seconds if the target type is instance or ip and 30 seconds if the target type is lambda. For Network Load Balancers, this is 10 seconds for TCP and HTTPS health checks and 6 seconds for HTTP health checks.
Healthy Threshold Count
The number of consecutive health checks successes required before considering an unhealthy target healthy. For Application Load Balancers, the default is 5. For Network Load Balancers, the default is 3.
Unhealthy Threshold Count
The number of consecutive health check failures required before considering a target unhealthy. For Application Load Balancers, the default is 2. For Network Load Balancers, this value must be the same as the healthy threshold count.
Health Check Path
CloudFormation Target Group
Listener
A listener is a process that checks for client connection requests, over a pre-configured protocol and port, and forwards requests to a target group by the means of a load balancer? A listener can be associated with a load balancer and only one. Rules can be defined for a listener that determine how the load balancer routes requests to the targets in one or more target groups. One listener is defined when the load balancer is created, and more listeners can be added at any time after that.
Listener Port
The port on which the listener listens for requests.
Listener Protocol
The protocol for connections from clients to the load balancer. For Application Load Balancers, the supported protocols are HTTP and HTTPS. For Network Load Balancers, the supported protocols are TCP and TLS.
Listener Rule
A listener rule is ... and associates a target group with the listener.
Default Listener Rule
There is a default listener rule. The actions for the default listener rules are declared in the configuration as "DefaultActions".
Action
Action Type
The action type is required, and it can be one of: "forward", "authenticate-oidc", "authenticate-cognito", "redirect", "fixed-response".
If the action is "forward", a target group must be specified by its ARN.